Si se pide a los analistas de seguridad que describan los puntos más problemáticos de su trabajo, sin duda obtendrán respuestas muy diversas. Una cosa que casi con toda seguridad tendrán en común es el reto de hacer frente a la fatiga de las alertas. Hemos observado que los retos en este ámbito se reducen a tres puntos dolorosos para los analistas:
- "No hay suficientes horas al día para atender el volumen de alertas que tengo encima".
- "Soy incapaz de utilizar eficazmente mi tiempo porque no puedo distinguir entre los falsos y los verdaderos positivos".
- "Me preocupa pasar por alto un ataque real porque la señal queda enterrada en el ruido de mi solución heredada".
Hay muchas razones que explican los puntos débiles descritos en las soluciones de seguridad heredadas, pero en gran medida se reducen a:
- La comparación simplista de condiciones y anomalías genera falsos positivos.
- Incapacidad de aprovechar las pistas contextuales de la red para mejorar la eficacia.
- Centrarse únicamente en las detecciones, y no en cómo organizarlas eficazmente para que un analista pueda centrarse en las cosas que realmente requieren su atención.
Una mejor opción para los analistas de seguridad:
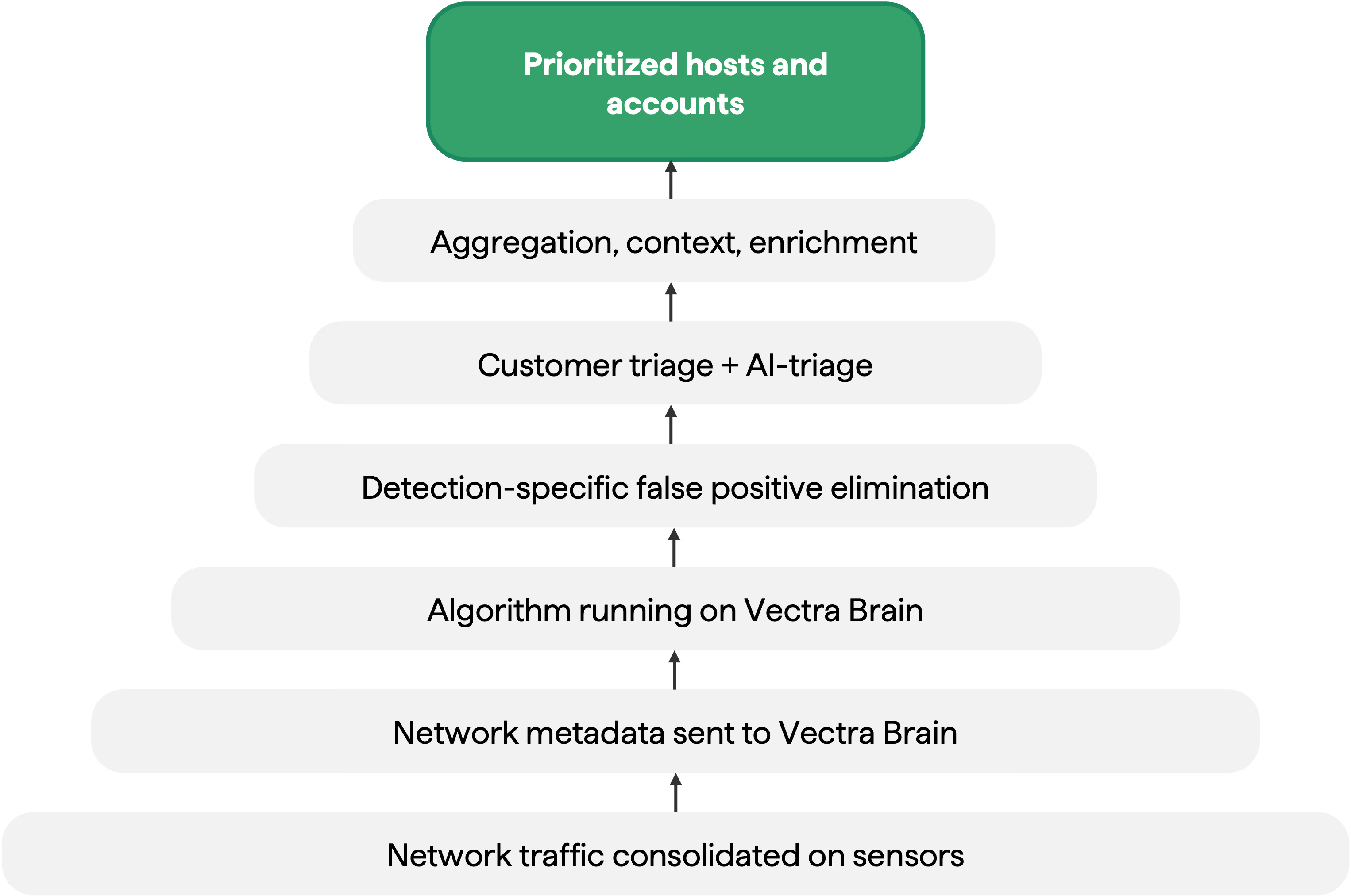
Desde el primer día, Vectra AI desarrollado sistemas de detección para eliminar la posibilidad de falsos positivos, dotando a los algoritmos de información contextual procedente de la red moderna. Mientras que los productos tradicionales de seguridad de redes pueden limitarse a buscar un patrón o una anomalía estadística sin tener en cuenta el contexto, Vectra AI sus sistemas de detección para aprovechar la información contextual de la red e identificar anomalías tal y como lo haría un analista de seguridad.
Por ejemplo, nuestra detección de fugas de datos en robos violentos aprende qué movimientos de datos son normales en cada subred, tiene en cuenta los sitios más visitados en su entorno y busca flujos de datos salientes anómalos, incluso en canales cifrados. Vectra AI correlaciona Vectra AI las detecciones entre entidades de host y de cuenta, aprendiendo el patrón e identificando cada objeto, y luego prioriza las detecciones para los analistas de forma práctica y ordenada por importancia. Esto simplifica enormemente el esfuerzo que supone operar Vectra AI con la competencia, que se limita a generar detecciones y deja que sea el analista quien descifre su significado.
Sin embargo, aún había un aspecto con el que no estábamos del todo satisfechos: el tratamiento de los falsos positivos. Esto se debe a que no todos los falsos positivos son maliciosos. También es posible detectar de forma fiable actividades cuyo comportamiento coincide con lo que indica el sistema; en el contexto en el que se produce un evento, puede tratarse de un falso positivo benigno en lugar de uno malicioso. Por ejemplo, algunos productos antivirus incorporan consultas de hash de archivos dentro de las consultas DNS al proveedor de antivirus. Este comportamiento puede parecerse mucho a un canal de comando y control que codifica datos dentro de la carga útil del DNS, y eso es porque lo es. Pero el hecho es que, aunque se trata de un auténtico túnel DNS, no es malicioso, sino benigno. Nuestra filosofía ha sido proporcionar visibilidad sobre estas detecciones de alta calidad de los comportamientos y métodos de los atacantes, pero equilibrando esto al priorizar únicamente las detecciones de alta confianza y correlacionadas a nivel de host o de cuenta para que el usuario les preste atención.
Esto nos llevó a plantearnos: ¿hay alguna forma de aplicar algunas de las mismas técnicas que utilizamos para impulsar nuestros algoritmos de aprendizaje automático e inteligencia artificial de primer nivel con el fin de ayudar a diferenciar entre los falsos positivos maliciosos y los benignos? El objetivo era eliminar en gran medida la necesidad de que nuestros clientes tuvieran que analizar los falsos positivos benignos, al tiempo que se daba prioridad a los falsos positivos maliciosos para que recibieran una atención inmediata. Así nació el «triage» con IA.
De forma similar al proceso que seguimos para crear nuestras detecciones, hemos incorporado capacidades de clasificación mediante IA analizando primero la metodología que aplican los analistas en la práctica para resolver estos problemas. A continuación, hemos entrenado nuestro sistema de aprendizaje automático e inteligencia artificial para automatizar la resolución de los casos con mayor nivel de fiabilidad.
Cómo funciona AI-Triage:
Como parte integrante de la Vectra AI , la clasificación mediante IA analiza automáticamente todas las detecciones activas del sistema, aprovechando el contexto de cada detección individual, así como los puntos en común entre ellas, para identificar casos de falsos positivos benignos que podemos clasificar automáticamente en nombre del cliente. Por ejemplo, si observamos que docenas de endpoints generan la misma detección de túnel HTTPS oculto hacia el mismo destino, durante al menos 14 días sin otros indicadores de compromiso, podemos identificar con seguridad que se trata de un falso positivo benigno. A continuación, AI-triage creará automáticamente una regla de clasificación en nombre del cliente, sin requerir el valioso tiempo del analista. Si un analista desea revisarla, la actividad sigue estando disponible en la plataforma, pero no requiere ninguna acción por parte del analista y no afecta a la puntuación del host ni de la cuenta.
Hemos observado que la clasificación mediante IA reduce en más de un 80 % el número total de alertas que, de otro modo, un analista tendría que investigar, lo que significa que se puede dedicar más tiempo a los incidentes que requieren la atención de un analista.
Despliegue con un solo clic
Ahora que conoce todas las ventajas que ofrece AI-triage, le alegrará saber que puede activar estas funciones con un solo clic. AI-triage no requiere ningún tipo de configuración ni gestión por parte del cliente. Para activarlo, solo tiene que ir a «Configuración» -> «AI-triage» y habilitar la función; en ese momento, AI-triage comenzará a ejecutarse en segundo plano para identificar detecciones de verdaderos positivos benignos con un alto nivel de fiabilidad y clasificarlas por usted.
En los 30 días transcurridos desde su lanzamiento, más de la mitad de nuestros clientes ya han activado la función de clasificación mediante IA. Estamos observando una reducción considerable de los falsos positivos benignos en la gran mayoría de los clientes. Sin embargo, esto es solo el comienzo de nuestro camino para aumentar la eficiencia de los analistas de seguridad. En próximas versiones, ampliaremos las capacidades de clasificación mediante IA para abarcar nuevos escenarios y otros productos de nuestra cartera.
Si desea más información sobre AI-Triage, consulte nuestro artículo de KB "AI-Triage en detalle": https://support.vectra.ai/s/article/KB-VS-1582
Para más información sobre la detección ML/AI de categoría mundial de Vectra, visite: https://support.vectra.ai/s/article/KB-VS-1285


.jpg)