Vectra AI ha publicado recientemente su informe «Estado de la detección y respuesta ante amenazas en 2026», que sigue la temática «Resiliencia en la era de la IA». La primera pregunta que me planteé cuando decidimos abordar ese tema para el informe fue: ¿qué conclusiones concretas del informe de este año revelan información sobre la resiliencia en 2026?
Para responder a eso, primero creo que debemos determinar qué entendemos por «resiliencia» o, en este caso, ciberresiliencia. Es un término que se utiliza con mucha frecuencia y creo que, por lo general, se aborda en un contexto y con un significado similares; sin embargo, siempre parece que la «resiliencia» es algo a lo que aspiramos o que esperamos alcanzar algún día. Y en materia de ciberseguridad, no creo que dejemos nunca de intentar alcanzar la ciberresiliencia. Sin duda, podemos tomar medidas para ayudar a que nuestras redes sean más resilientes, como comprender nuestra exposición al riesgo o agilizar los procesos para poder reaccionar más rápido ante las amenazas; pero entonces surge una nueva amenaza o vulnerabilidad y dejamos de ser resilientes hasta que la hayamos abordado.
Lo mismo ocurre en la vida. Puedes tomar todas las medidas adecuadas para asegurarte de que estás sano o de que tu casa está protegida, y luego adoptas una nueva mascota. De repente, tus cortinas están hechas trizas y faltan los zócalos, y no tenías ni idea de que tu hogar no fuera a resistir a una criatura tan inocente.
Para mí, la resiliencia es nuestra capacidad para recuperarnos, reponernos o, simplemente, volver a ponernos en pie y seguir funcionando cuando se producen incidentes. Nuestras redes no son una excepción. Y resulta que las redes actuales entrañan riesgos que se mueven a la velocidad de la IA; de hecho, según un informe de CrowdStrike, los ciberataques son un 65 % más rápidos gracias a la IA.
¿Cuál es la situación actual de la detección y la respuesta ante amenazas en la era de la IA?
Descarga gratuita: Estado de la detección y respuesta ante amenazas en 2026: resiliencia cibernética en la era de la IA
Ya que estamos en la era de la IA, ¿no sería mejor preguntarle a ChatGPT?
La respuesta sería algo así como: «El estado actual de la detección y la respuesta ante amenazas en la era de la IA es una carrera entre atacantes que utilizan la IA y defensores que se valen de la IA, en la que el éxito depende de detectar señales de ataque basadas en el comportamiento en los ámbitos de la identidad, cloud y la red antes de que los atacantes puedan desplazarse lateralmente».
Sin embargo, deberíamos preguntar a los profesionales de la seguridad, que viven esta realidad a diario, cuáles son los detalles reales de lo que ocurre realmente dentro de sus redes. Y ese es precisamente el motivo por el que seguimos publicando el informe «State of Threat Detection and Response». Este año, 1 450 profesionales han respondido a preguntas sobre todo tipo de temas, desde la frecuencia con la que se dejan de lado tareas de seguridad importantes, hasta la eficacia de las herramientas, el uso de la inteligencia artificial y su impacto, la visibilidad encloud híbridos ycloud , así como otras áreas. Echemos un vistazo a lo que dicen los defensores sobre algunas de las áreas que afectan directamente a su capacidad de resiliencia.
Exposición al riesgo: ¿quién y qué hay en la red?
Una de las preguntas que hemos planteado a los defensas en cada uno de los tres años en los que Vectra AI ha publicado este informe es: ¿cómo calificarías tu visibilidad en diversos entornos híbridos?
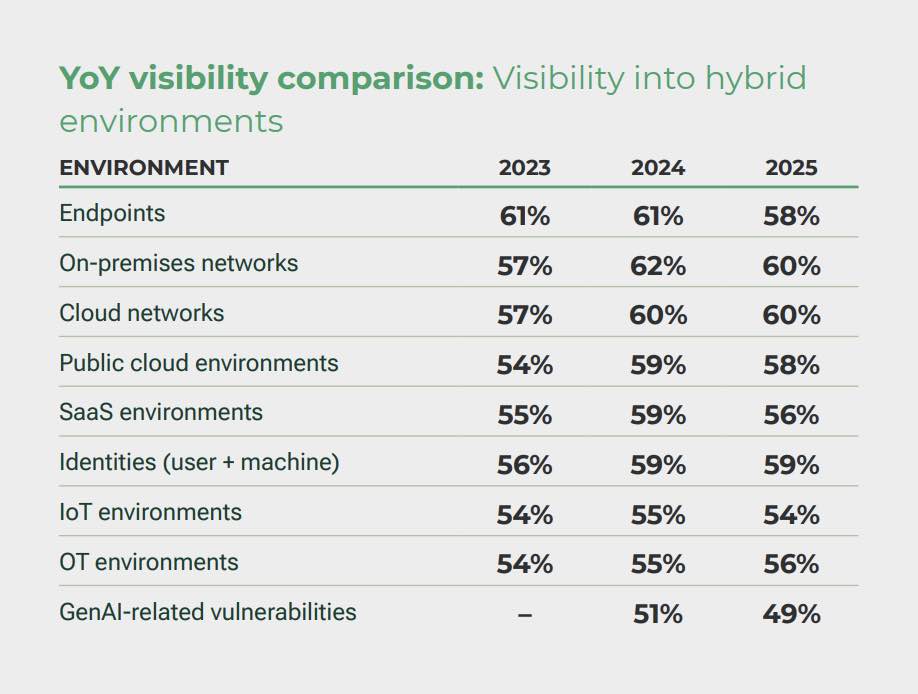
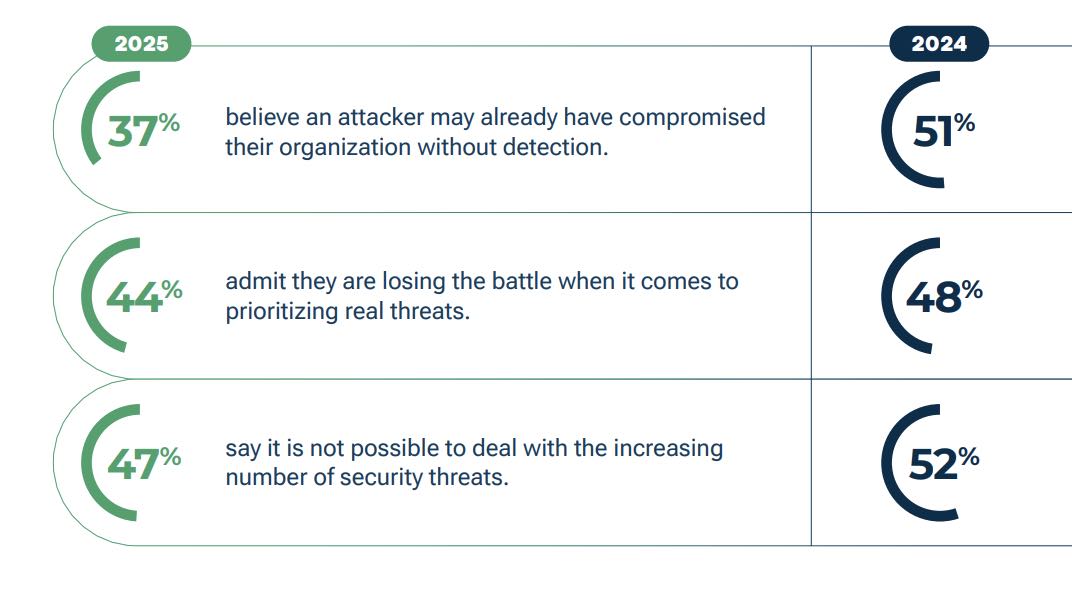
No es solo que los defensores carezcan de una visibilidad completa de sus entornos; si además se tiene en cuenta el número de herramientas que utilizan para la detección de amenazas y la respuesta a las mismas en dichos entornos, el 39 % de ellos maneja más de 20 herramientas. La ciberresiliencia requiere visibilidad de las redes y no estamos viendo mucha mejora, si es que hay alguna, de un año a otro, lo que indica que no todos los defensores saben quién y qué hay en su red. De hecho, el 37 % cree que un atacante puede haber comprometido ya su organización sin que ellos lo sepan. ¿Se debe esto, en parte, al gran número de herramientas que se utilizan, a que el ruido sigue siendo un problema o a que la visibilidad parece fragmentada entre demasiados flujos de telemetría?
¿Saben los defensores qué comportamientos indican un riesgo?
Entre los profesionales de la seguridad encuestados, el 44 % admite que está perdiendo la batalla a la hora de dar prioridad a las amenazas reales.
Al analizar los datos, empiezas a vislumbrar algunas razones que lo explican, y quizá la principal tenga que ver con la latencia de detección.
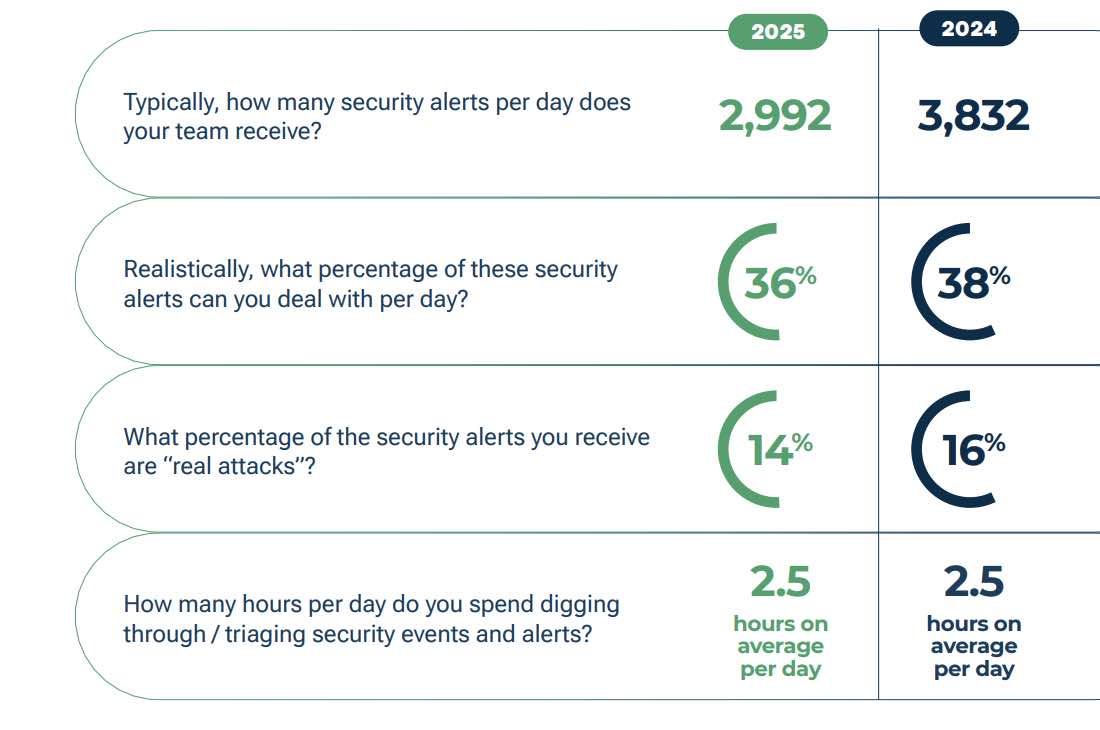
Además de las dos horas y media que los responsables de seguridad dedican cada día a la clasificación de alertas, el 71 % afirmó que deja de lado tareas de seguridad importantes al menos dos días a la semana, y que solo puede gestionar algo más de un tercio de las alertas que recibe cada día. Cuesta imaginar que, en este contexto, la latencia resulte útil para detectar qué comportamientos de riesgo existen en una red.
¿En qué aspectos se puede mejorar la seguridad de la red?
Preguntamos a los responsables de seguridad qué aspectos son importantes a la hora de evaluar soluciones. El 72 % mencionó la reducción de riesgos, la adecuación a los requisitos normativos y la eficacia operativa cuantificable. El cumplimiento normativo es el aspecto más obvio, ya que los equipos de ciberseguridad suelen desempeñar un papel fundamental a la hora de garantizar que los controles cumplan los requisitos normativos; y, aunque el informe no profundiza demasiado en ninguna de estas áreas, se pueden extraer algunas conclusiones al respecto.
Seguimos observando que la opinión de los defensores respecto a los proveedores de seguridad apenas mejora.

¿Podemos vincular la «eficacia operativa cuantificable» con la opinión que tienen los clientes de los proveedores? Quizá no de forma directa, pero los responsables de seguridad están demostrando que quieren poder demostrar la eficacia de sus soluciones, aunque no creen necesariamente que los proveedores estén cumpliendo con su parte del trato.
Sin embargo, el 67 % está de acuerdo enque la implementación de herramientas basadas en la inteligencia artificial está teniendo un impacto positivo en la capacidad de identificar y hacer frente a las amenazas. Lo mismo ocurre aquí: esto no se traduce necesariamente en una «reducción del riesgo», pero los responsables de la seguridad señalan los ámbitos en los que, en su opinión, se están produciendo mejoras positivas.
¿Se está quedando atrás la ciberresiliencia?
Los responsables de seguridad informan de un aumento de la confianza. Por ejemplo, el 37 % cree que un atacante podría haber comprometido ya su organización sin que ellos lo supieran, un porcentaje que ha bajado desde el 51 % registrado el año pasado. Además, los defensores informan de una experiencia global positiva con el uso de la IA en el SOC; de hecho, el 87 % espera utilizar más herramientas de IA el próximo año para sustituir a las herramientas tradicionales de detección y respuesta ante amenazas. Los defensores también quieren que la IA se encargue de tareas como la clasificación de alertas y las funciones de investigación, lo que podría conducir a mejoras en los retos de latencia de la detección, pero la IA por sí sola no hará que las organizaciones sean más resilientes por arte de magia; serán los defensores quienes lo consigan.
A juzgar por lo que nos indica el informe, sí, la ciberresiliencia se está «quedando atrás» en ciertos ámbitos, sobre todo si tenemos en cuenta que existe una exposición al riesgo y que la priorización de las amenazas sigue siendo un reto. Todavía hay demasiadas alertas que quedan sin atender, demasiadas lagunas de visibilidad y demasiadas herramientas y proveedores que no están a la altura, pero no estamos diciendo a los defensores nada que no sepan ya: ellos son quienes ya están trabajando para hacer frente a la exposición, los riesgos y los retos de seguridad que nunca cesan.
Descarga el informe «Estado de la detección y respuesta ante amenazas 2026»hoy mismo.


